CoSoSys

As one of the world’s leading developers of cross-platform Data Loss Prevention (DLP), eDiscovery, and Device Control solutions, CoSoSys offer IT security solutions that truly make an impact.
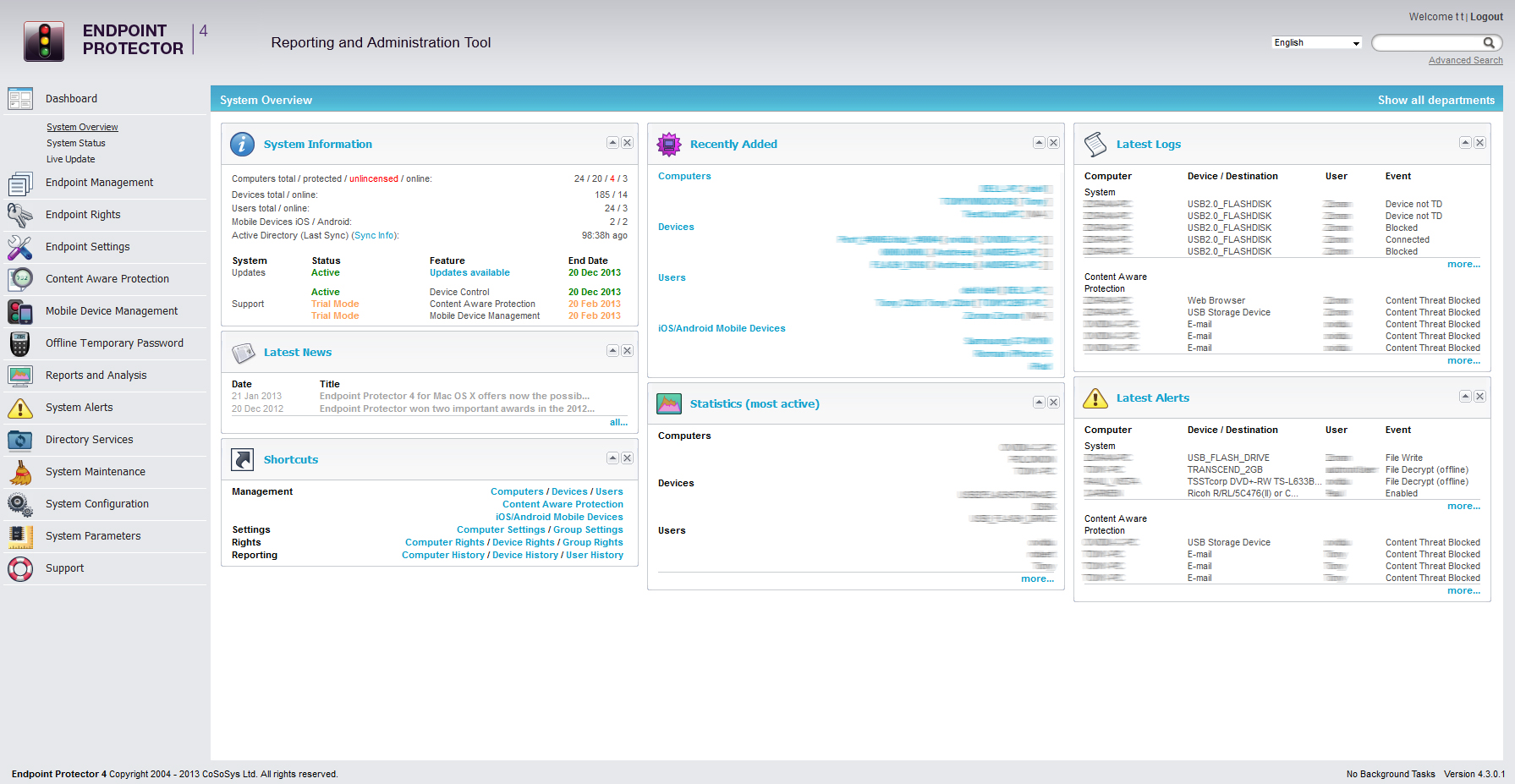
CoSoSys’s main product, Endpoint Protector, has been adapted and fine-tuned over a number of years to face the challenges of new technology and data security needs. Endpoint Protector has a strong focus: protecting companies’ endpoints against data threats such as theft, loss or leakage.
Endpoint Protector, is an advanced all-in-one DLP solution for Windows, macOS, and Linux as well as Thin Clients, that puts an end to unintentional data leaks, protects from malicious data theft and offers seamless control of portable storage devices. Its content filtering capabilities for both data-at-rest and in-motion, range from predefined content based on dictionaries regular expressions, to profiles for data protection regulations such as GDPR and HIPAA.
Data Loss Prevention
Device Control
eDiscovery
Encryption Control
CoSoSys is focused on protecting customers data with the additional benefit of device control (a vital tool for many businesses and a solution that some of the new era vendors do not offer). The technology avoids complicated, time-consuming deployments and provides full control over sensitive data.
More data protection, less headaches.
With Endpoint Protector you avoid complicated, time-consuming deployments and make sure your DLP solution doesn’t get disruptive for legitimate business.
- Fast, remote client deployment
- Protect sensitive data (even while working offline)
- Outside Network and Outside Hours policies
- Simplified deployment process
- Central administration
- Protect company IP, PII, financial data, and more
- Insider Threat Protection
- Award-winning technology
Talk to a Cyber Advisor
Looking to protect your data? Request a callback to speak to one of our cybersecurity specialists today.

Device Control
USB & Peripheral port control
Define granular access rights for removable devices and peripheral ports and establish policies for users, computers and groups – maintaining productivity while enforcing device security.
Content-aware DLP
Scanning data in motion
Prevent data leakage through all possible exit points, from clipboard, screen captures and USB devices, to applications including Microsoft Outlook, Skype or Dropbox.
Data Mapping & eDiscovery
Scanning data at rest
Prevent data breaches by scanning and identifying sensitive data at the endpoint level on Windows, macOS, and Linux computers. Ensure compliance with regulations like HIPAA, PCI DSS and others.
Enforced Encryption
Automatic USB encryption
Encrypt, manage and secure USB storage devices by safeguarding data in transit. Password-based, easy to use and highly efficient.